Frost & Sullivan: Brand Protection Report
Uncover the latest trends and proactive measures to protect your organization's digital assets.




Identify risks faster and scale offensive security across your entire attack surface with a community of trusted security experts that takes Pentest as a Service (PtaaS) further.

Combat risk in real-time with proactive security testing from the leaders in Pentest as a Service (PtaaS). Scale your security team with on-demand access to expert talent. Our powerful platform and proven experience, let you test security controls across your attack surfaces with greater ease and efficiency. It’s the testing approach you need to remediate smarter.
Enhance your agility and accelerate innovation by gaining real risk insights with on-demand security resources. Cobalt enables a scalable response and risk remediation without the need to expand your workforce. With our comprehensive approach, you can address current challenges and adapt for future demands.
Safeguard your applications. From secure code review and pentesting to dynamic application scanning, we help you ensure your applications are compliant, robust, and threat-resistant.
Protect your network from cyber threats. Pinpoint vulnerabilities, assess risk, and enhance your security operations to safeguard sensitive data and ensure business continuity.
Manage security controls across all of your cloud services, including AWS, GCP, or Azure. Quickly identify vulnerabilities and weaknesses, gain insights, and get actionable recommendations for remediation to minimize risk.
Safeguard your brand reputation by assessing risk from an attacker’s point of view. Anticipate where breaches might happen and swiftly respond to potential data leaks to protect your brand integrity.
Make sure your devices aren't a vulnerable attack surface. From hardware, to firmware, to radio communication vulnerabilities, we help you identify weak points across your device ecosystem.
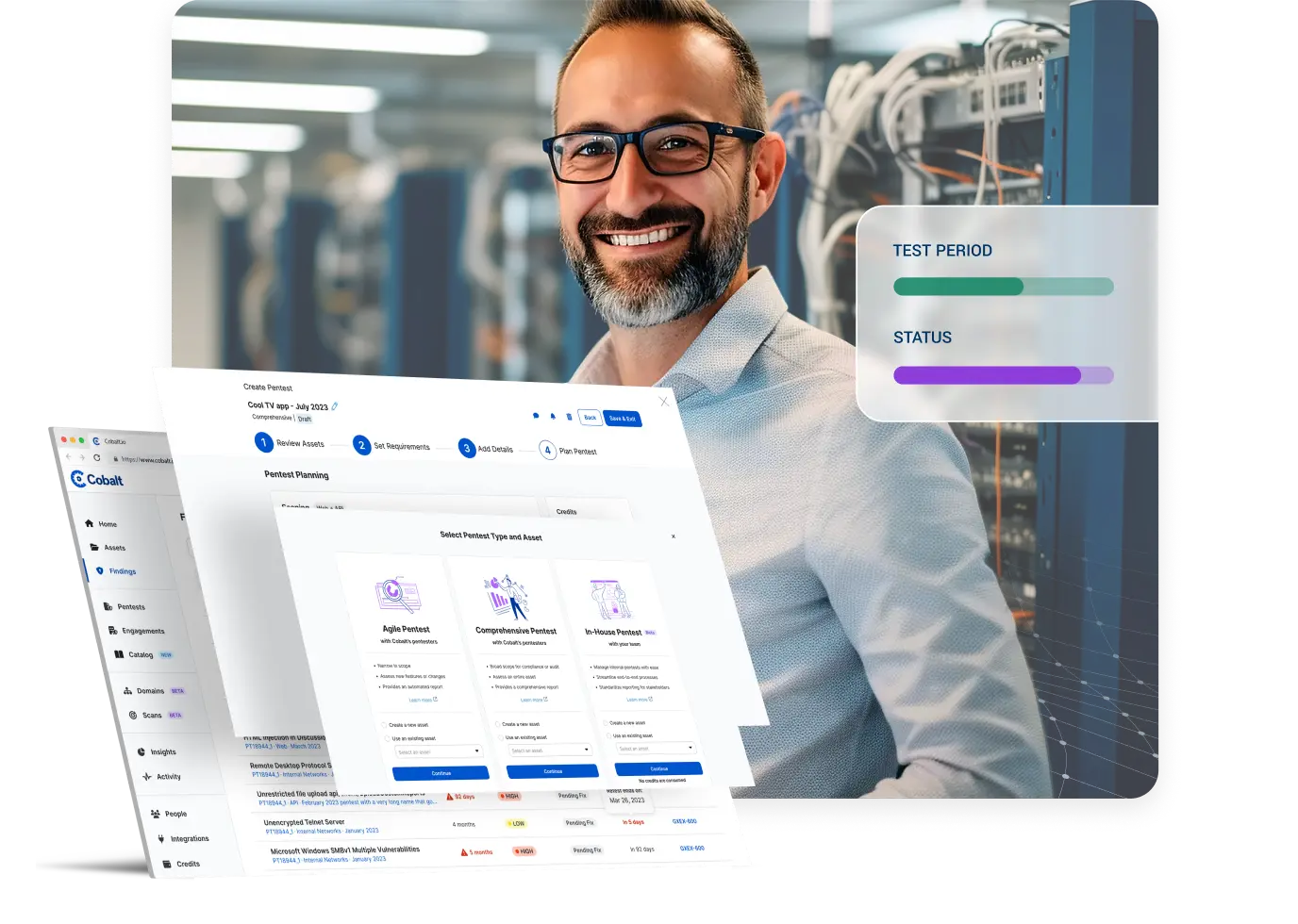
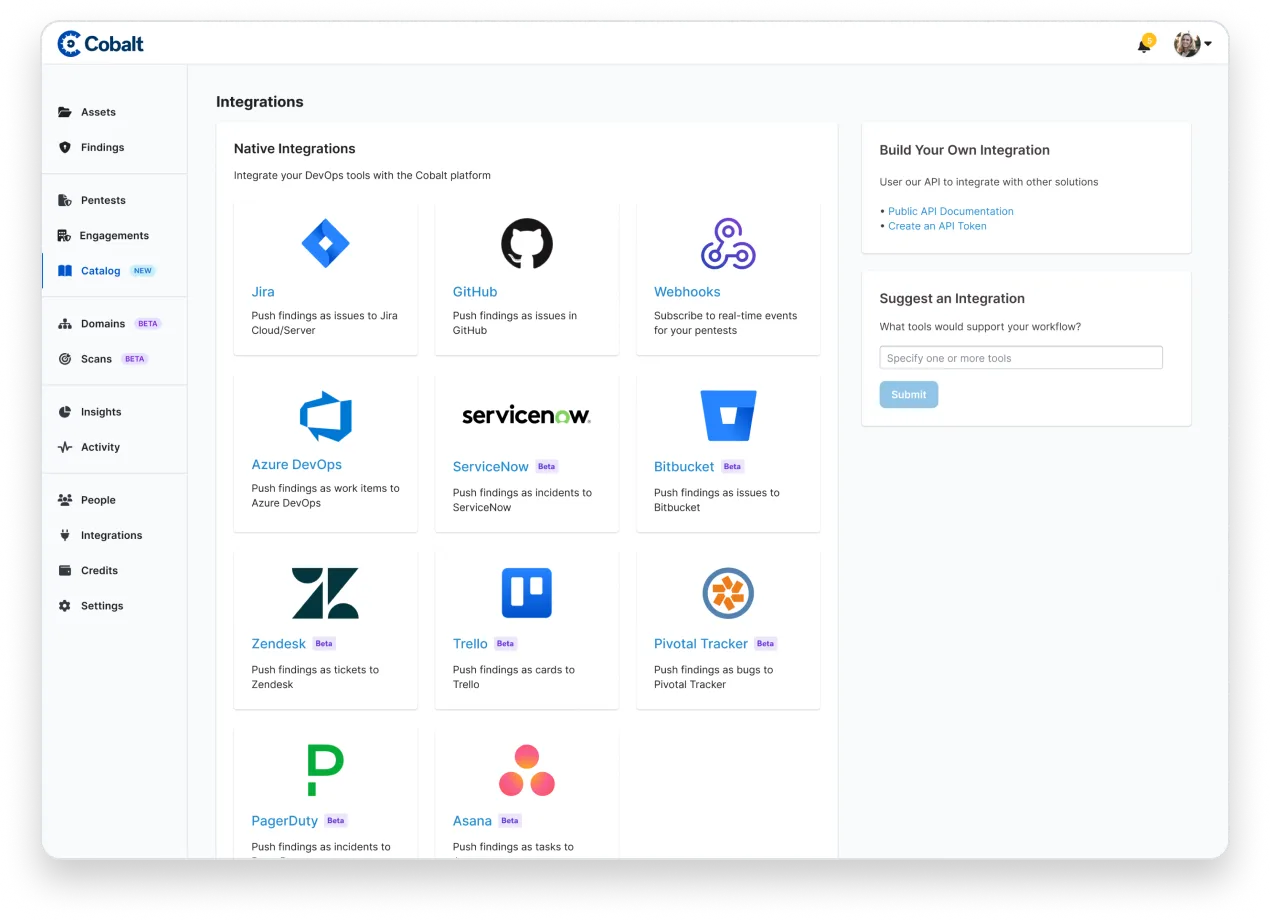
Scale your pentest program and effectively manage data across workflows with technology integrations.
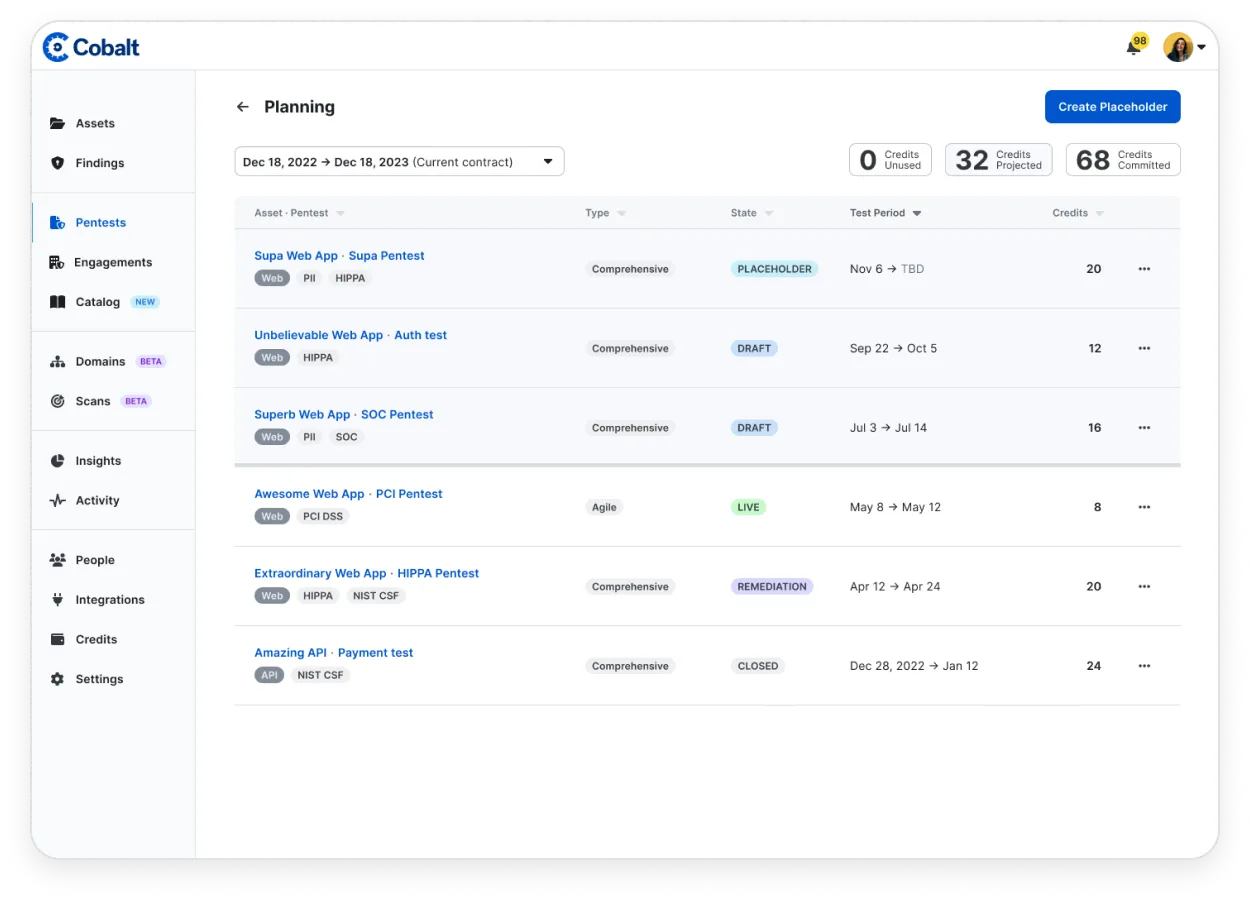
Automate tedious steps in the testing process while bringing in human insight and perspective where it matters most. Start testing faster and simplify planning for future testing needs.
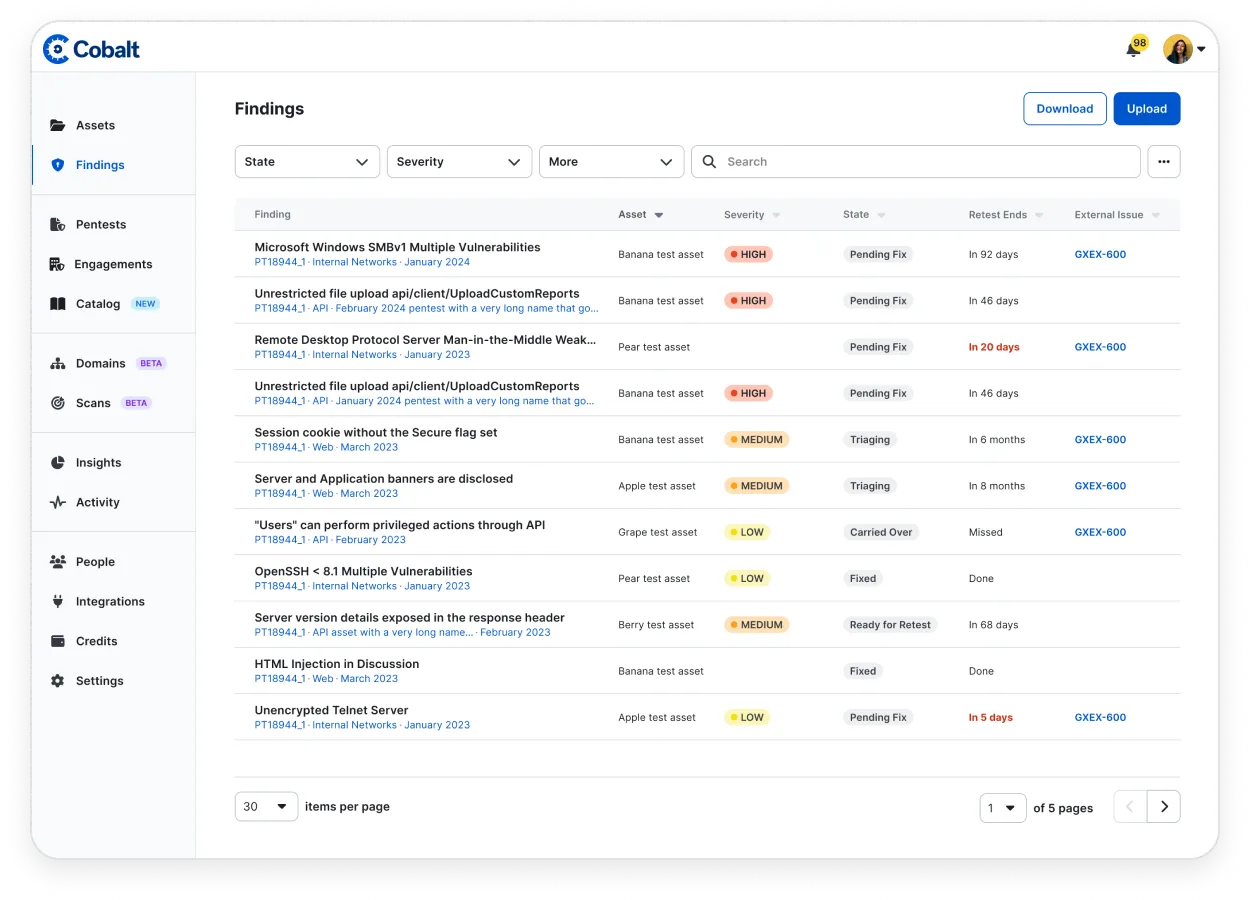
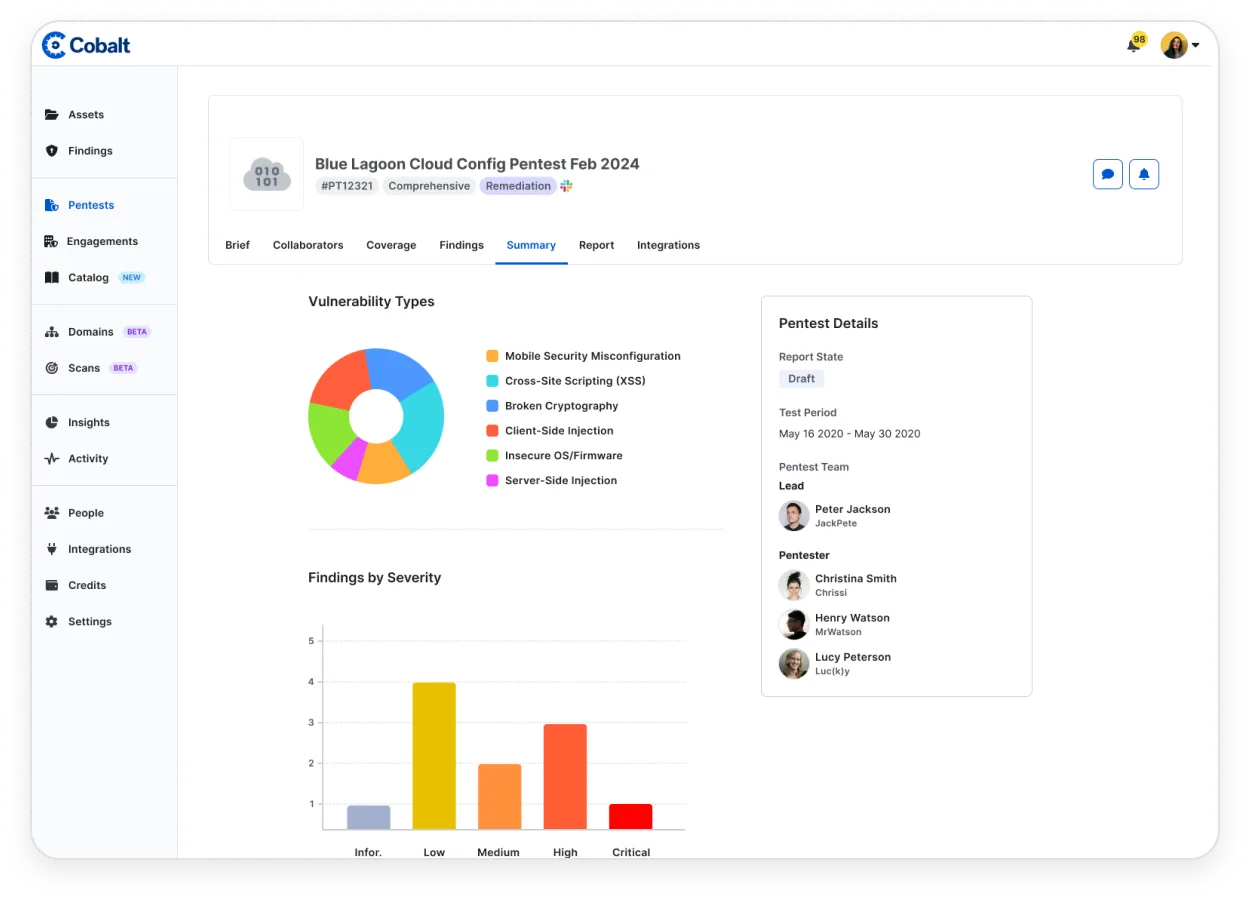
Increase program efficacy and optimize forward momentum with insight into historical progress and trends.
Whatever security testing projects you’re tackling, our simplified consumption model makes them easier to manage.


"One main benefit is the variety of skill sets that you're able to tap into because Cobalt has a community of pentesters that you can readily draw from. We don't have to hire more red team people, we can bring them on as needed"

“The main benefits that we get from Cobalt are speed, scalability, and repeatability. We’re able to quickly launch and execute pentests; and beyond that, we’re able to see individual findings in real-time and relay them to the engineering team so they can start triaging immediately.”

"Being able to interact with findings in the platform and discuss them through Slack makes for a much more efficient process. We’ve been able to get into it and engage with the findings there, which is a big improvement on the old process."
The Cobalt platform is purpose-built for continuous security engagements. Our understanding of attack surfaces and intuitive technology platform give you the power to get started quickly and accelerate find-to-fix cycles.

Cobalt gives you access to a worldwide community of vetted experts aligned with the unique needs of your business. Whatever the asset or your specific requirements, we find the right fit for your business.

Mitigate future risk, secure your infrastructure, and make the most of your resources with a centralized approach. Empower your security and development teams to take quick action with unprecedented visibility. And make improvements over time with ongoing test data and analytics.

Empower your security and development teams with Cobalt’s unique combination of a modern SaaS platform and our community of vetted security experts. Trust the pioneers of PtaaS as your offensive security partner across your entire attack surface.